Understanding Proof of Work (PoW): The Engine of Blockchain Security
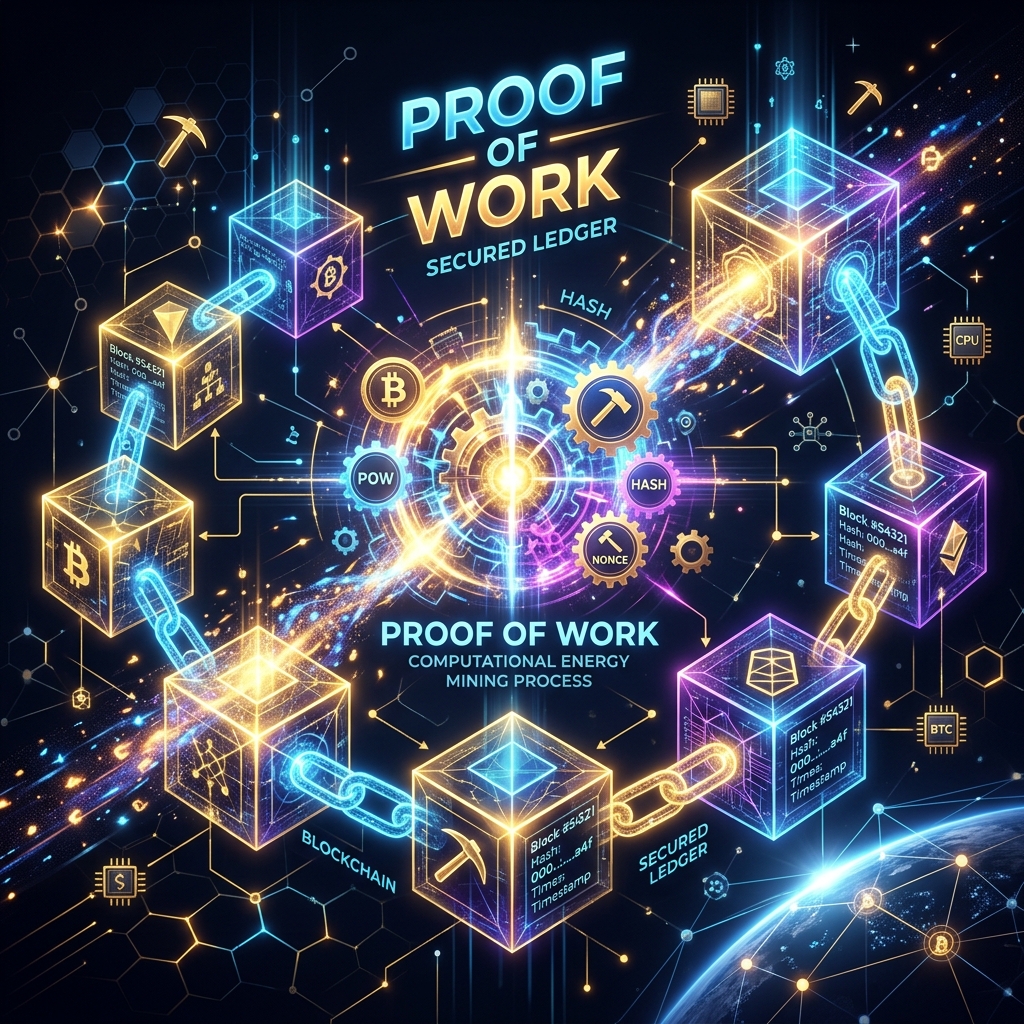
Proof of Work (PoW) is the original consensus mechanism used in blockchain technology, most famously by Bitcoin. It is a system that requires a participant (miner) to perform a significant computational effort to secure the network and validate transactions.
In this post, we will dive deep into how PoW works, why it is important, and its detailed workflow.
1. What is Proof of Work?
At its core, Proof of Work is a piece of data that is difficult (costly, time-consuming) to produce but easy for others to verify. It acts as a defense against malicious attacks, such as Distributed Denial of Service (DDoS) or spam, by making the cost of the attack prohibitively expensive.
In a blockchain, PoW ensures that everyone agrees on the current state of the ledger without the need for a central authority.
2. The Detailed Workflow of PoW
The process of “mining” is essentially the execution of the Proof of Work algorithm. Here is how it works step-by-step:
Step 1: Transaction Bundling
Miners collect pending transactions from the network’s memory pool (mempool). These transactions are bundled together into a “candidate block.”
Step 2: Adding a Nonce
Each block header contains a field called Nonce (Number used once). This is a random number that miners change repeatedly to find a specific result.
Step 3: Hashing the Block
The miner passes the entire block header (including transactions, the previous block’s hash, and the nonce) through a cryptographic hashing algorithm (like SHA-256 for Bitcoin).
Step 4: Meeting the Difficulty Target
The network sets a “Difficulty Target” — a specific value that the resulting hash must be below.
- If the hash is higher than the target, the miner changes the Nonce and tries again.
- This process happens trillions of times per second (Hash Rate).
Step 5: Finding the Valid Hash
When a miner finally finds a hash that meets the target, they have “found the block.” This is the “Proof” that they have performed the necessary “Work.”
Step 6: Network Verification
The miner broadcasts the block to the network. Other participants (nodes) can verify the hash almost instantly. If valid, the block is added to the blockchain, and the miner receives a reward.
3. Why Use Proof of Work?
| Feature | Description |
|---|---|
| Security | Extremely resistant to tampering. To alter a block, an attacker would need 51% of the network’s power. |
| Decentralization | Anyone with hardware and electricity can participate in securing the network. |
| Trustless | No central bank or company is needed to verify if a transaction is real. |
4. Pros and Cons
Pros:
- Proven security track record for over a decade.
- Encourages decentralization through competitive mining.
- Incentivizes miners to protect the network.
Cons:
- High Energy Consumption: Requires massive amounts of electricity.
- Hardware Waste: Mining often requires specialized ASIC chips that become obsolete quickly.
- Scalability: Slower transaction speeds compared to Proof of Stake (PoS).
Summary
Proof of Work is the foundation that made decentralized digital currency possible. While newer mechanisms like Proof of Stake are gaining popularity for their efficiency, PoW remains the gold standard for pure, untamperable security in the crypto world.