JWT Session Token Implementation: Stateful vs. Stateless
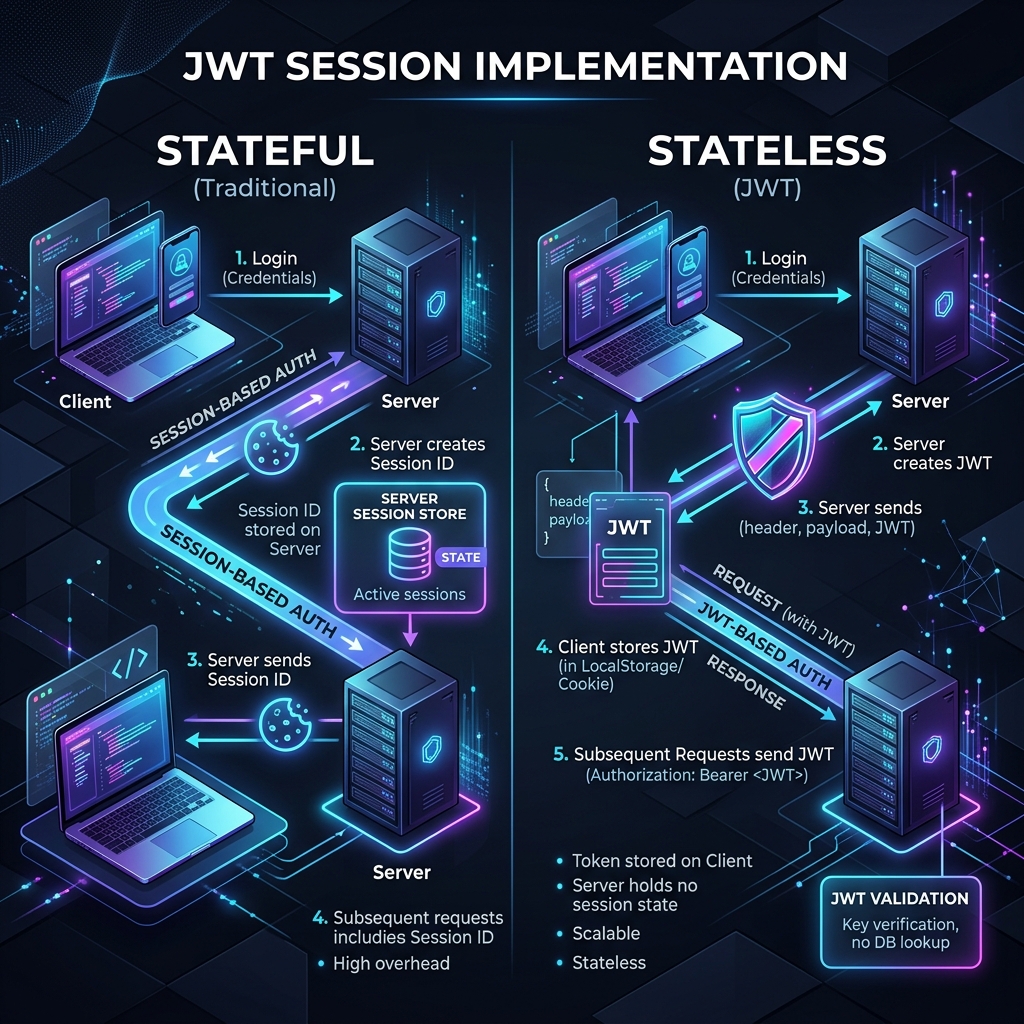
JSON Web Tokens (JWT) have become the industry standard for securely transmitting information between parties as a JSON object. When it comes to session management, developers often face a critical architectural decision: Should the implementation be Stateless (without state) or Stateful (with state)?
Both approaches have their merits, and choosing the right one depends entirely on your application’s scale, security requirements, and infrastructure.
1. Stateless JWT Implementation
In a purely stateless implementation, all the session data (user ID, roles, expiration) is stored directly within the JWT itself. The server does not need to store any session information in a database or cache.
How it Works:
- The user logs in.
- The server generates a JWT containing user details and signs it with a secret key.
- The server sends the JWT to the client.
- For every subsequent request, the client sends the JWT.
- The server verifies the signature and trusts the data inside without checking a database.
Pros:
- Scalability: Since the server doesn’t need to look up session data, it’s easier to scale horizontally across multiple servers.
- Performance: Reduces database/cache latency on every request.
- Decentralization: Ideal for microservices architectures where different services can verify the token independently.
Cons:
- Revocation Issues: Once a token is issued, it is valid until it expires. Revoking a specific token before its expiration (e.g., if a user logs out or is banned) is difficult without introducing some state.
- Token Size: Storing too much data in the JWT can lead to large headers, increasing the overhead of every HTTP request.
2. Stateful JWT Implementation
A stateful implementation combines the portability of JWTs with the control of traditional sessions. In this model, the JWT usually contains a unique session ID, and the server maintains a record of active sessions in a data store (like Redis or a SQL database).
How it Works:
- The user logs in.
- The server creates a session record in the database and generates a JWT containing the session ID.
- The server sends the JWT to the client.
- For every request, the client sends the JWT.
- The server verifies the signature AND checks the database/cache to ensure the session is still valid/active.
Pros:
- Instant Revocation: You can immediately invalidate a session by deleting it from the database.
- Better Control: Easy to implement features like “Log out of all devices” or monitoring active user counts.
- Security: If a token is stolen, it can be blacklisted immediately.
Cons:
- Reduced Scalability: Every request requires a database or cache lookup, which can become a bottleneck.
- Infrastructure Overhead: Requires maintaining a highly available session store.
3. Which One Should You Choose?
| Feature | Stateless JWT | Stateful JWT |
|---|---|---|
| Scalability | High | Medium |
| Revocation | Difficult | Instant |
| Complexity | Low | High |
| Performance | Faster | Slower |
Use Stateless JWTs if: You are building a high-traffic API where horizontal scaling is the top priority and short token lifetimes (with refresh tokens) are acceptable.
Use Stateful JWTs if: Security is paramount, and you need the ability to immediately kick users off the platform or manage multiple active sessions per user.